![]()
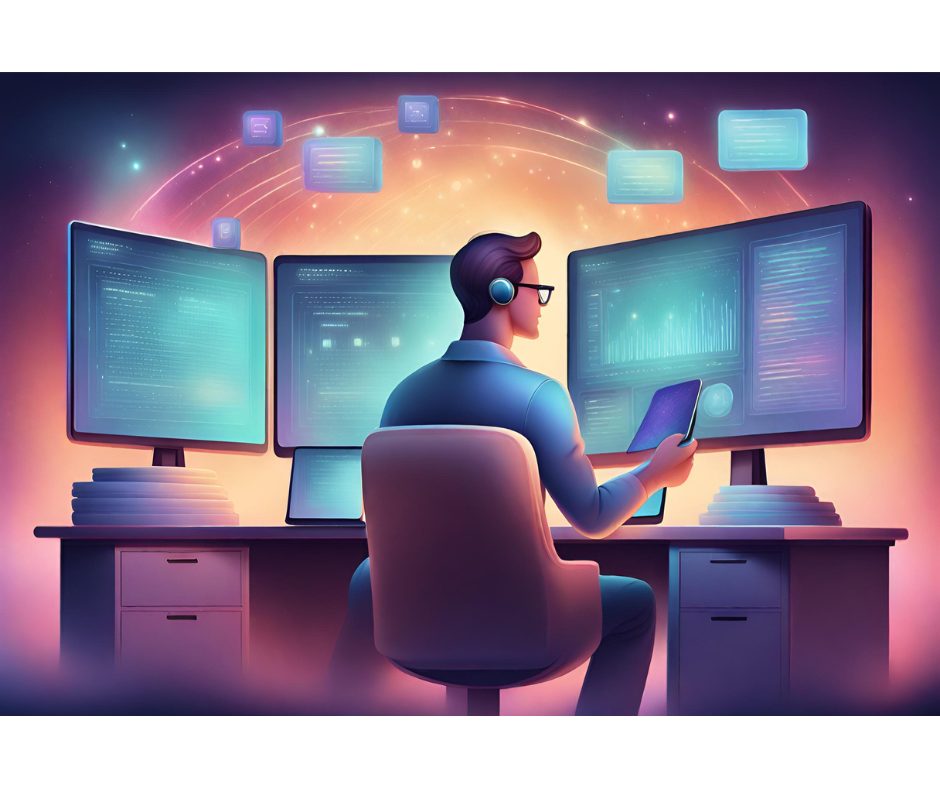
You’ve long been on the lookout for hackers who want to do harm to your systems and damage—or steal—your data. But what if the felon you should fear, now or in the future, is standing next to you? Or works at one of your chief competitors? Here are three cases where top technology executives are accused of stealing trade secrets. And it’s a growing problem.
SSF imported auto parts works out of a nondescript building just off the main retail drag in South San Francisco, Calif. In a space half the size of a football field sit rows of metal shelves filled with brake discs, alternators, water pumps and other components for Audi, Mercedes-Benz, Porsche, Saab and Volvo cars. Workers in blue shirts move briskly about, picking and packing parts for delivery overnight to repair shops and dealerships around the country.
Yes, this is a warehouse. But it is also a center for what some security experts worry is a new type of computer crime: Digital espionage. By top technology executives.
SSF’s computer systems were repeatedly broken into over seven months starting in early 2001. An FBI agent who investigated the incident said he believed large portions of SSF’s electronic catalog of 20,000 car parts were copied, so rivals could build a better catalog. The culprits? The chief technology officer, chief executive officer and a computer consultant for a rival: Dallas European Parts Distributors of Carrollton, Texas. According to the U.S. Attorney’s Office in San Francisco, the trio became criminals when they accessed SSF’s computers without authorization and illegally trafficked in SSF computer passwords.
Statistics are not kept by federal law enforcement agencies on the number of acts of espionage committed each year by executives and technology managers in this age of worldwide computer networking. But research by Baseline has identified a half-dozen cases of digital espionage that are alleged to have been committed by corporate chief technology officers and information-technology directors in the past two years. The alleged spies include:
- The chief technology officer at Business Engine Software Corp. in San Francisco, who pled guilty in July to downloading trade secrets, such as information on customers and products in development, from rival Niku Corp. in Redwood City, Calif.
- The information-technology director at Lightwave Microsystems in San Jose, who was indicted in May 2003 on charges of stealing the network equipment maker’s Manufacturing Execution Database and other secrets, stored on backup tapes. His alleged intent: sell the secrets to competitor JDS Uniphase. He pleaded not guilty.
- The chief technology officer of Speedera Networks, a Santa Clara, Calif., provider of Web hosting and content delivery services; according to a civil suit filed in California Superior Court in Santa Clara County, he allegedly broke into a database at Keynote Systems to steal performance data about Akamai Technologies, a Cambridge, Mass., competitor. Speedera denies any wrongdoing.
- The CEO of Orbit Communications, a satellite data reseller, who allegedly recruited technology security consultants to attack the Web sites of three of Orbit’s competitors, according to an FBI complaint. The CEO is a fugitive.
- The former network and information-technology manager at Manufacturers Electronic Sales Corp. (MESC), a sales representative in Santa Clara, Calif., for electronic component makers. The manager pleaded guilty in August to breaking into the company’s computer system from his new employer. He was charged with downloading a customer database, reading e-mail and deleting data, then destroying evidence of the break-in.
These incidents, say security experts such as Steve Orrin, vice president of security and technology at Watchfire, which provides software and services to help companies manage online security, privacy and compliance risks, portend a new and worrisome threat for corporations. The people in U.S. companies who are responsible for safeguarding networks and the secrets they hold about products, customers and strategies—CTOs and I.T. managers—may be using their skills to cross the line into crime.
“And it’s probably one of the most flagrant violations of trust,” he says, “when the people you trust to defend your networks turn around and execute something that could put your organization at such significant liability.”
This may just be the next evolution of the economic spy.
“The average computer professional has as much, if not more, skill than [the typical corporate hackers] going out and committing crimes,” says Ira Winkler, a top I.T. security consultant and author of the forthcoming book Spies Among Us: How to Stop the Spies, Terrorists, Hackers, and Criminals You Don’t Even Know You Encounter Every Day.
“The cases speak for themselves,” adds Christopher Sonderby, who heads up the computer-hacking and intellectual-property unit in the U.S. Attorney’s office in San Francisco. “The cases would seem to support the notion, certainly, that it has been done and that it’s a real risk.”