It’s hard enough to protect sensitive data within a large corporation when that data is well defined and easy to locate. Think customers’ credit card numbers, Social Security numbers and other customer data, or internal documents like human resources files on employees, tax and other finance documents.
But sensitive data isn’t always arranged in easy to recognize patterns the way credit-card or Social-Security numbers are, according to Alex Tosheff vice president and chief information security officer for online credit-processing company BillMeLater.com, which allows customers to shop online using information that identifies them personally, but doesn’t involve a credit card or any account numbers at all.”
“We went through a long process of classifying our data, and create policies around it and got buy-in from the people we need to, and educated people about how we were actually classifying data, and had tools to keep that stuff from getting out [across the Internet],” Tosheff says.
“But we still knew we were probably communicating things we shouldn’t be,” he says. “Things that were going out in [instant messaging] or through other channels people used because it was easier to do their jobs that way, but that were probably not the channels we would have chosen.”
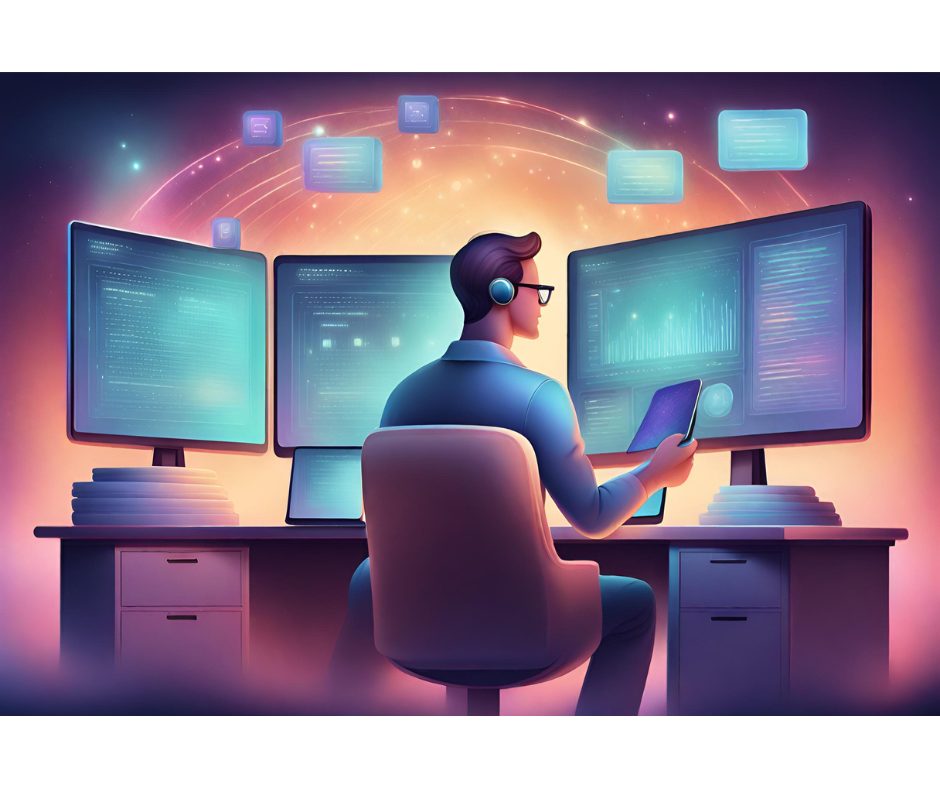
Tosheff addressed the problem with a set of data-loss prevention products from Reconnex. Rather than going out on the Internet to search documents, Reconnex products search all the data on an internal company’s network and, more importantly, search and index all the data going out of the company through e-mail or other formats, through the company firewall.
The products, which are built into a special-purpose appliance that’s designed to be dropped onto a network builds an index of all the information a company communicates through the Internet, no matter in what format it’s sent.
Tosheff declined to identify the kinds of data he discovered leaking through his company’s firewall, specifically because it was sensitive.
“There were a number of cases where we had people sending out information that would be OK, usually, except the were doing it through IM or other channels that weren’t as secure as they should be,” he says.
But it’s not surprising that sensitive data will leak, even from companies that rely heavily on structured data and don’t have much trouble defining what kinds of data need to be protected, according to Deven Bhatt, chief security officer of airline of Airlines Reporting Corporation (ARC), a clearing house for flight data and ticket purchases that serves more than 150 airlines and train companies as well as thousands of travel agencies and other partners.
“Of course you have your structured data, credit cards and [Personally Identifiable Information] and you can build filters for that,” Bhatt says. “But this appliance approach can help you scan your hard drives and data on your networks and know what data you have and who is using it, and then how it’s leaving your organization.”