Bill Tyson was excited to see how his latest brainstorm, an insurance policy that protected customers against identity theft, was faring.
As the chief marketing officer for AGIA Insurance Services, he had found a creative way to sell what he thought was a poorly understood product—one that would repay consumers for the costs of having their identities forged and misused by online miscreants, and provide credit monitoring and other protective tools.
Tyson’s direct mail campaign had already failed, but he figured that was because the customers AGIA was targeting—members of the Good Sam Club and the National Rifle Association—were more likely to be reached on the Net than through snail mail. With higher-than-average incomes, they would likely be worried about having their personal information stolen and misused. He also decided that an e-mail campaign was a cheaper and more effective way to reach these potential victims, just in time for the Christmas buying season.
Like any conscientious marketing executive, Tyson opened an e-mail promoting the insurance. He clicked on the link embedded in the message, expecting to be directed to a Web page with educational videos discussing the consequences of identity theft and an offer to buy insurance online. Instead, he got an eyeful: a Brazilian Web page hurling insults at President Bush. AGIA’s own Web site—hosted by a third party the company was using while its own servers were being upgraded—had been hijacked.
“They didn’t let us know,” Tyson says. “That was the big aha. If I had not brought it to their attention, would I have ever known? … It left me feeling vulnerable.”
Aghast, he immediately severed AGIA’s relationship with the hosting company, which he declines to name, and pulled the project in-house. But the incident underscores important lessons for companies that handle sensitive customer information, particularly smaller companies like AGIA. They must fiercely protect the integrity of their systems and networks, even when it means stretching limited resources to do so. How was AGIA supposed to build a business on protecting consumers from identity theft if it couldn’t protect itself?
Just this year, far bigger companies than AGIA have suffered serious security breaches. In March, for example, GMAC Insurance informed customers that their personal data had been stolen by thieves who took two computers from a regional office.
Although U.S. losses from cybersecurity breaches declined to $141.5 million from $201.8 million, according to the 2004 Computer Crime and Security Survey released in June, viruses and denial-of-service attacks replaced intellectual property theft as the biggest costs.
The attack on the hosting company did not expose AGIA’s customer data, but Tyson worried that AGIA’s credibility could end up in shreds. Also, why should he believe what AGIA’s information-technology department was telling him? In his previous job as head of JLT InterActive, the U.S.-based e-business consulting division of British insurance broker Jardine Lloyd Thompson Group, Tyson and the chief technology officer had hired a white-hat hacker who exposed vulnerabilities with user registration and authentication before the system was deployed.
AGIA is not a household name, but many of its clients are well known. The 48-year-old company, based in Carpinteria, Calif., sells, markets and administers insurance programs on behalf of groups such as the Good Sam Club and the American Legion. AGIA insures about 2 million people, or about 5% of the aggregate membership of these affinity groups, professional societies and other organizations. It also hosts and manages over 50 Web sites for some of these clients.
Tyson joined AGIA in July 2003, lured by CEO John Wigle, the son of AGIA’s founder, to do “new and innovative things.” That directive included using the Internet to expand the business. The insurance industry is conservative and resists transacting business online—AGIA sells most of its policies through direct mail and advertisements, supported by call centers and the Internet. Still, customers want to buy services like emergency travel assistance online, and AGIA needed to be ready when and if the industry shifted to the Web.
Tyson didn’t expect his new job to be too daunting. At JLT InterActive, which he founded, he was working on creating community portals for unions and trade groups before JLT stopped funding the division after Sept. 11.
Yet, the identity-theft hack spooked Tyson. Though he dealt with that incident by dumping the Web host, he thought that AGIA’s Web sites and systems were not performing as well as they should, nor were they as secure as he would like.
For example, customers could not download brochures or access encrypted forms. No one at AGIA knew when servers were down unless they physically checked. Furthermore, a consulting firm Tyson had hired after he arrived, the Comdyn Group, told him that some of AGIA’s coding techniques were out of date.
More and more, the company was fielding questions from clients and prospective clients, particularly financial partners, about how often it checked the security of its servers and what it was doing to proactively mitigate security threats.
Like other insurers, AGIA is subject to a host of security and privacy regulations. These include the federal Health Insurance Portability and Accountability Act, which requires companies to write a security policy and prove they are following it, as well as a California law that mandates companies to tell residents of that state when their personal information is compromised.
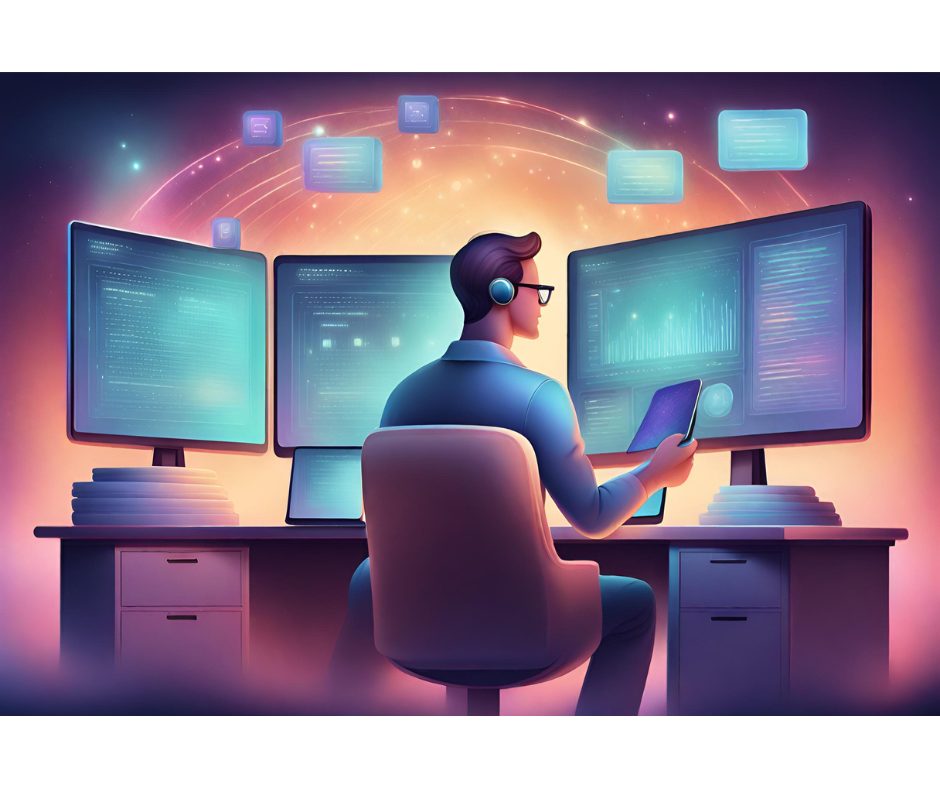
At the same time, cyberattacks were becoming more severe. The SQL Slammer worm in January 2003 was followed by the Blaster worm on Aug. 11 and the Sobig.F virus on Aug. 19. In response, 10 employees, including Tyson, were spending up to 10 hours each week scanning the Web for information on vulnerabilities and manually patching software as quickly as they could, an expensive and ineffective use of their time.
Without being able to prove that AGIA was securing its network on an ongoing basis, Tyson might have trouble attracting new clients. In fact, the company risked losing existing ones if they felt their customer information was in jeopardy—even though Tyson insisted that it was protected.
However, Tyson could not make AGIA more secure all by himself. For that he needed cooperation from Garry Boswell, the new director of information technology, but Boswell was slammed with work. Boswell had been in his job for about three months, did not report to Tyson, and had just taken over a project to install a Cisco voice-over-Internet Protocol phone system so AGIA could more easily report call center statistics to clients. The project was demanding—Boswell discovered that he had to replace switches and routers throughout the company.
On top of that, Boswell was updating AGIA’s security policy, which dictates how the company responds to security threats in compliance with federal regulations. He was well aware of the Comdyn Group’s report, and he was simultaneously installing antivirus software and evaluating new security products from some of the 500-plus vendors on the market for possible installation in 2005.