By Andrew Serwin
Five years ago, cyber-security wasn’t an issue that was on many people’s minds. Now, concern over such issues is at an all-time high. Unfortunately, that attention may have given us tunnel vision on what cyber-security really is, and the risk it presents.
However, the rise of the Internet—specifically Internet-enabled devices—can give us a road map to the future of cyber-security.
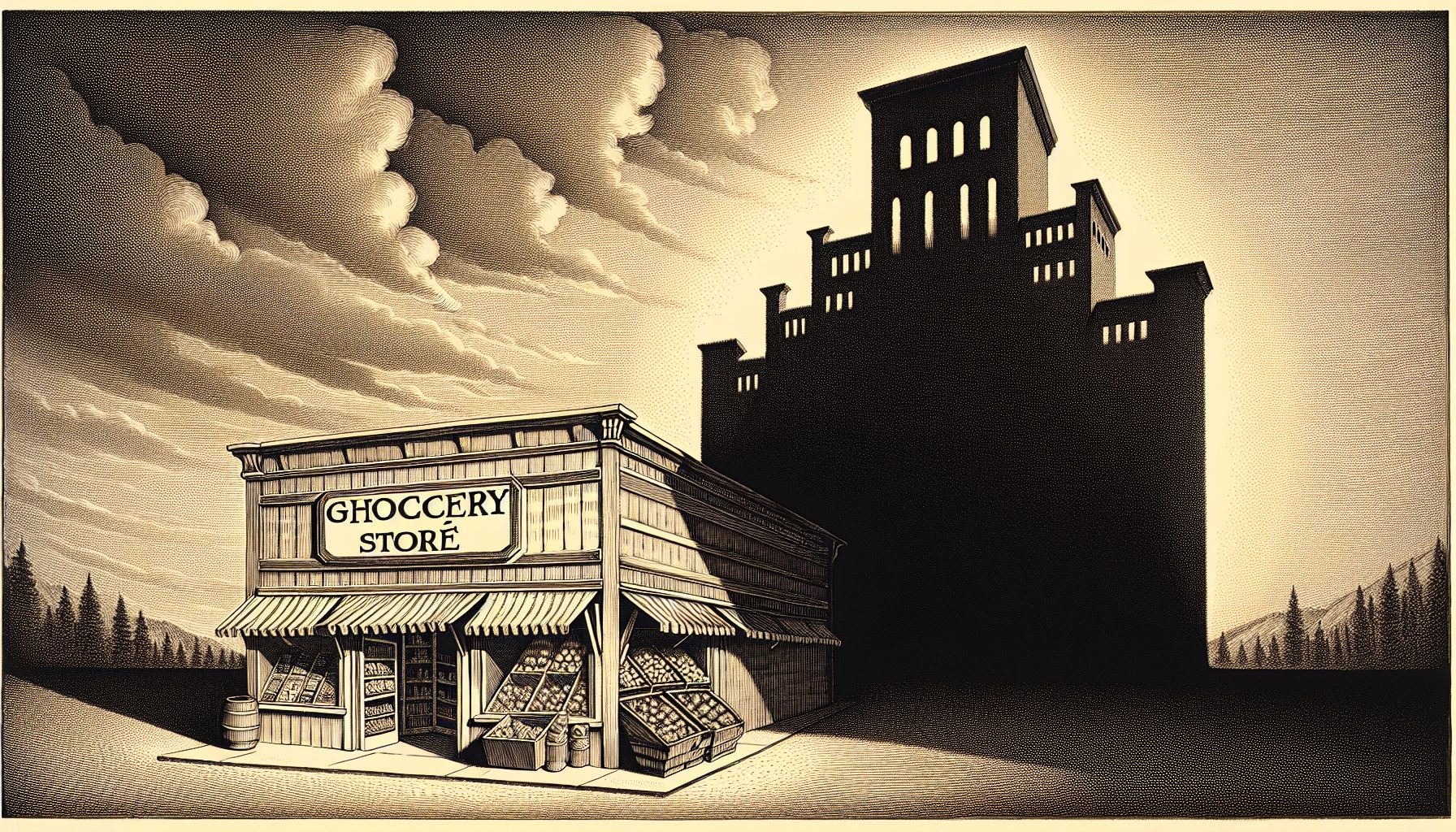
The Internet started as its own ecosystem that was, in essence, parallel to existing business models. The Web was the Web, and traditional brick-and-mortar businesses were not focused on it and did not see it as a threat.
For example, I am certain that when the Internet began, video rental stores didn’t think it would be a competitor, let alone a disruptive competitor that would fundamentally change how we consume video. Yet here we sit, using devices that existed before—such as televisions and DVD players—but that now have Internet-enabled capabilities to access content we used to rent in the physical world.
In essence, we moved from a world in which the Internet was separate from traditional businesses into a world that uses Internet-enabled devices.
We’re now moving into a world that employs even more Internet-enabled devices, and the future holds further technological advances that expand the Internet into areas we can’t fully imagine.
Connectivity’s Troubling Implications
The backbone of this expansion is its ubiquitous connectivity. That’s a wonderful thing in many ways, but it has troubling implications we are only beginning to understand. As more systems came online, more money began changing hands via electronic commerce. That drove criminals to become cyber-criminals, because there was money to steal.
When the Internet first gained traction, very few people imagined that electronic connectivity between systems could become a way for nation-states to conduct massive intelligence operations. Yet, here we are in the “post-Snowden” world where many countries are trying to expand their cyber-attack capabilities.
In some ways, this brings them as much street credibility globally as nuclear weapons did for emerging nation-states in the 20th century. And, probably no one in 2000 thought terrorists might actively seek weapons that could be deployed exclusively through electronically connected systems.
Yet, here we are, recalling attacks such as the 2012 hack into Saudi Aramco. CNN reported that “in a matter of hours, 35,000 computers were partially wiped or totally destroyed … and one of the most valuable companies on Earth was propelled back into 1970s technology, using typewriters and faxes.”
The way to conceptualize this problem is: We are all in the same pipe now. Everyone—from teenagers obsessively using social media, to multinational companies whose existence depends on connectivity, to nation-states and terrorists seeking to exploit intelligence, gain economic advantage or damage critical systems, and everyone in-between—effectively uses the same transmission system, or pipe, to conduct both business and their personal lives. This is reality today.
Where Cyber-Security Will Have to Go
In light of that reality, it’s important to look at the early development of the Internet to understand where cyber-security will have to go. Right now, although people are starting to understand that it’s an issue most companies should consider, it’s still seen as a discrete issue that’s important only for certain kinds of companies—ones that rely more on technology, have certain forms of data or are government contractors.